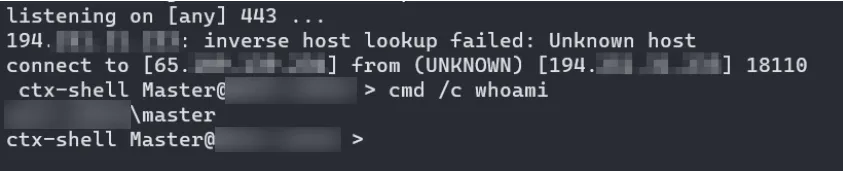
SilverBullet is a tool I made for internal red teaming purposes. It is a simple C2 reverse-shell client, that is able to bypass most publicly available enterprise EDRs. At first this project was just a simple proof-of-concept, but it has evolved into a powerful tool that I’ve used in multiple red teaming engagements.
Doing the “impossible”
This whole project started after I was challenged as a joke to bypass a specific XDR. I started to research the XDR and found some loop-holes in it. A few days later I had a working prototype that was able to bypass the XDR. After the initial success, I started to research other EDRs and found out that the same trick worked on many of them.
After the initial findings, I contacted some EDR vendors and disclosed the exploit method to them. Most of the vendors were really helpful and made the necessary changes to fix the issues.
Development continues
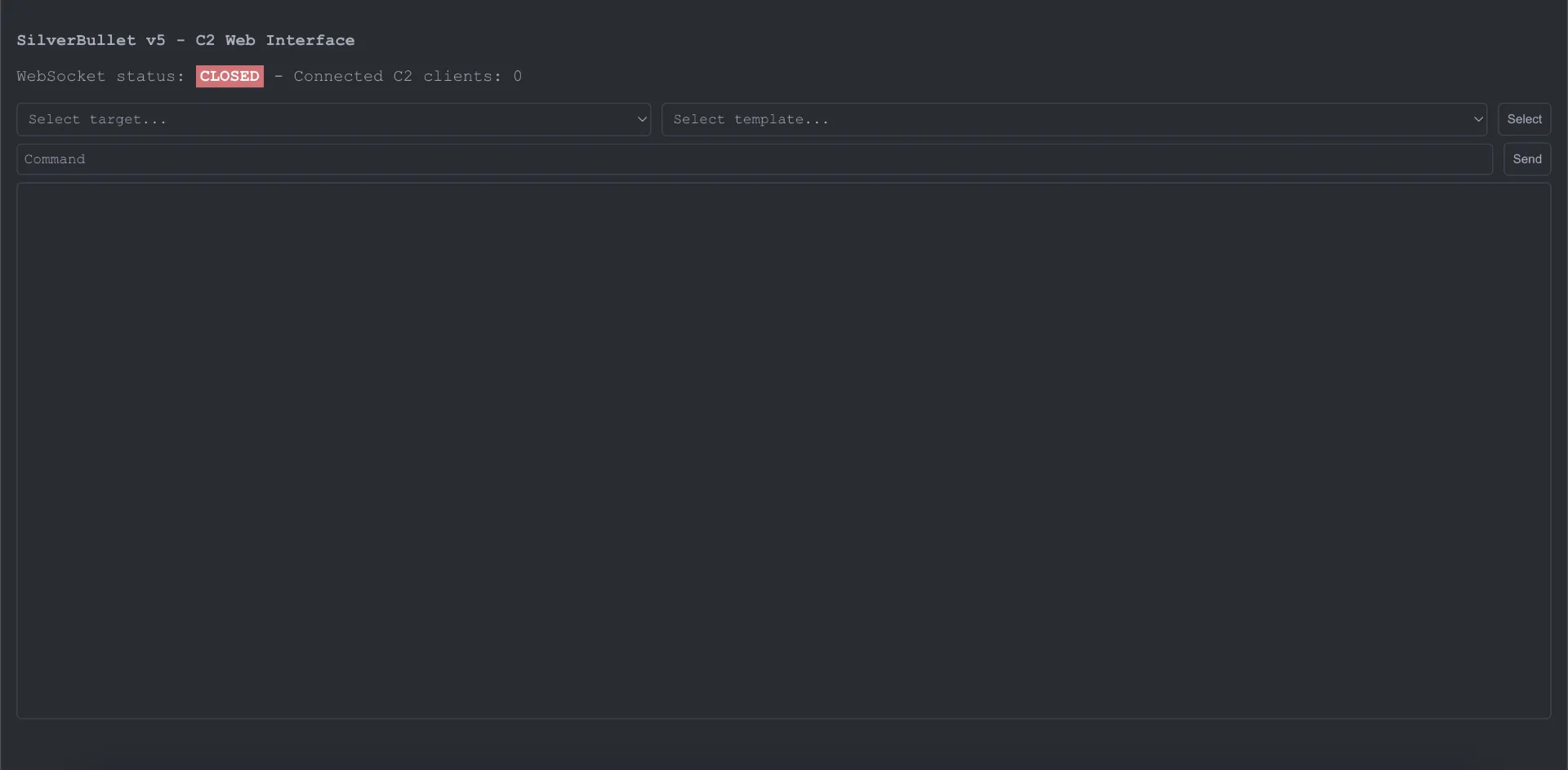
Now, after over a year of development later, SilverBullet has evolved into a powerful tool that I’ve used in multiple red teaming engagements. The current version has a simple web dashboard for managing the clients and sending commands. The dashboard also has a list of predefined commands for some common tasks. The latest version also supports multiple different C2 protocols to avoid detection.